Turnkey provides the infrastructure to create and manage wallets, sign transactions, and secure cryptographic keys at scale. Every signing operation happens inside hardware-backed secure enclaves — private keys are never exposed to Turnkey, your application, or your team.Documentation Index
Fetch the complete documentation index at: https://turnkey-0e7c1f5b-graham-docs-revamp.mintlify.app/llms.txt
Use this file to discover all available pages before exploring further.
How Turnkey works
Instead of managing private keys directly, Turnkey abstracts key management into a layered system. Your application is a parent organization, and sub-organizations are available to fully isolate wallets, users, and policies per end user or tenant. Every action — signing, creating wallets, updating permissions — is evaluated by a policy engine running inside a hardware-backed secure enclave before anything executes. Keys never leave the enclave. Turnkey returns signed payloads and supports transaction broadcasting directly to the network. Turnkey operates based on a shared responsibility model. Turnkey is responsible for the security of the platform itself, including enclave infrastructure, policy engine correctness, key confidentiality, and service availability. You are responsible for securing your integration: configuring your root quorum, scoping user permissions, authoring policies, and managing credentials. See the full model for details.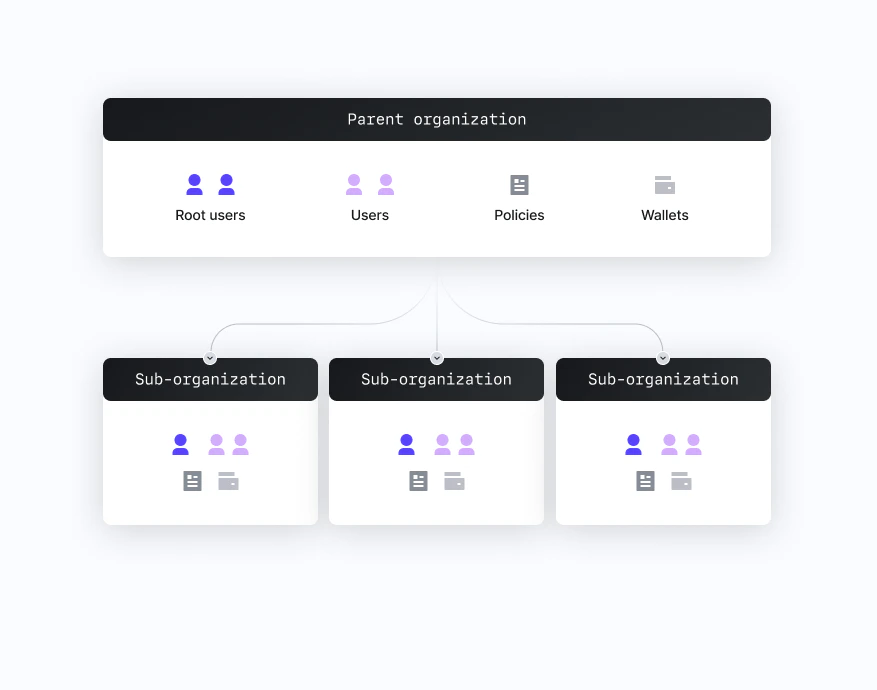
Core concepts
- Organization — Top-level entity representing your application. Contains users, wallets, and policies.
- Sub-organization — Fully isolated organization nested under the parent, typically representing an end user or business customer. Parent orgs have read-only access and cannot modify sub-org contents.
- User — A resource within an org or sub-org that submits activities via a valid credential. Users can have tags, which policies reference for role-based controls.
- Root user / root quorum — Root users can bypass the policy engine. A root quorum sets the approval threshold required to exercise root permissions.
- Authenticator — A credential used to stamp API requests: passkeys, API keys, email OTP, or OAuth.
- Activity — Any action submitted to Turnkey (sign transaction, create user, update policy). All activities are evaluated by the policy engine.
- Policy — A logical rule that evaluates to ALLOW, DENY, or REQUIRES_CONSENSUS. Controls who can sign what, under what conditions.
- Wallet — An HD wallet (seed phrase) that generates multiple accounts across chains. Lives inside the enclave; only addresses and signatures are returned.
Where to start
- Explore by use case — Embedded Wallets, Company Wallets, Key Management
- Account setup — create your org and API key
- SDKs — client libraries for React, React Native, Swift, Kotlin, Flutter, and more
- Security — how the enclave model works and what Turnkey’s security guarantees are
- AI-ready docs — use Turnkey docs with Cursor, ChatGPT, or your own LLM tooling